The loss of the physical component in an event defined as theft is not always the most important thing to take note of, especially in the cases of digital devices like laptops or smartphones. Your personal data still present on the stolen hardware component should give you more reason to worry.
Nevertheless, it is not always all doom and gloom. A good number of manufacturers have taken precautions and gone the extra mile to protect the information of people who purchase their devices if they ever lose their stuff. We are talking about encryption here because it is easily the best form of protection you can get for your data.
If thieves somehow manage to succeed in getting away with your device, they might start using it. They could even sell it. Or perhaps, they could auction its parts. One thing they would be unable to do, however, no matter how hard they try, is to access your personal data if you have used some form of encryption.
Pro Tip: It is possible to fix many PC issues by using the PC Repair tool. PC Repair is easy to use and reliable Windows optimization software developed to fix hundreds of system issues.
Special offer. About Outbyte, uninstall instructions, EULA, Privacy Policy.
Even if we were to consider the events that come before they start using your device, we expect that they would at least erase its content. Of course, they cannot do this if it is password protected, or unfortunately, in some cases, they might manage this feat successfully if your password and its setup are not equipped with the highest levels of security.
- If you are using a device manufactured by Apple, then we believe that you would be fine in the vast majority of scenarios. Activation Lock is available on this maker’s platform at least. Regardless, what we just inferred does not hold true for every top digital device maker in case you are wondering.
- If your laptop, for example, is running the Windows operating system, then, unfortunately, the thieves would have things a lot easier for obvious reasons. Encryption is not really one of the strong points of Windows, is it? It is not Microsoft’s forte either. Perhaps, things are that way on the platform because of its maker’s behavior. You will find out more about this soon enough
Now we will examine how the scenarios would play out when a user loses a device manufactured by different firms or an item based on a specific platform. Sit tight while we guide you through everything.
How to protect your data in case your smartphone gets stolen?
We would begin here with an iPhone as our base device or reference item. We will make comparisons to other mobile devices and platforms similar to the one this smartphone runs on.
- Apple (iOS):
By default, Apple enables secured encryption on its mobile devices. If you lose your iPhone, the person that gets hold of it would be unable to access your phone because that individual probably does not know your password. This protection remains intact even when you have opted for Face ID or Touch ID in place of the traditional numeric or alphabetic combination password or pin setup.
Nevertheless, we understand that they are some users do not use even use any passcode or pin to prevent unauthorized access to their device in their everyday life. We cannot speak as to why they do this though but we hold the view that is wrong to do so.
And for others who use a passcode so weak or one incredibly easy for an adversary to guess, we have to say what they have done is as pointless as it sounds. If you are going to use a combination of numbers like 0000 or 1234, then you might as well not use a passcode. You are only making the job of thieves easier by giving them more incentives to steal your device.
We also have to implore on the fact that sometimes some information or details remain visible when a smartphone is stolen even when its owner has used a passcode or a good protection setup. You can always ensure that this is not the case if you ever lose your device by configuring your notifications not to show when your device is locked.
If you ignore the setup that allows the stated flaw to thrive, then the thief might do more than just selling your device. With some research and a little bit of work, then he/she can request SMS messages to reset the passwords or PINs for accounts or profiles that control very sensitive details and items. You surely would not want this to happen.
You have to worry about incoming calls too. In most cases, thieves cannot do much with this functionality, but we are not holding our breath. We can go on and on about other things adversaries could do if they ever lay their hands on your smartphone, but we expect you to have gotten our point by now.
If you lose your device, we recommend that you head to the website for the Find My iPhone utility to locate your iPhone or iPad. If you want to prevent the person that stole it from using it (and you should), you can make use of the Lost Mode option there. This selection disables all notifications and alarms on your smartphone. There are also other options you can make use of to help you find the stolen item.
You can put up a message to show on your device display stating that whoever finds the device (if the person is a bit nice and not an individual whose morality is negotiable) should PLEASE contact you to return it. You can even leave a phone number for communication purposes.
If the person who got hold of your phone does not intend to give it up, then you might find things a lot more difficult to handle. If you finally give up on retrieving your device, then you should get rid of all the data on it for obvious reasons. This act is an ideal one in most scenarios, and it just works fine. Even if the thief puts off your device, IOS will carry out the required operation once it comes back on.
- Google (Android):
The scenario plays out the same way for people who have Android devices. As far as we know, at least, on modern ones. Google confirmed that encryption had become a functionality enabled by default since Android 7.
The same risks exist though: an Android-powered smartphone would continue to show messages or notifications when it gets stolen unless the user has otherwise taken the necessary precautions to ensure that this does not happen.
Similar protection schemes are employable on the Android platform: The equivalent to Apple’s Find My iPhone would be Google’s Find My Device. The latter possesses more or less the same functionality as the former. You can use it to stop your phone from displaying your messages or notifications to the thief, wipe the data on your device remotely, and so on.
How can I protect my data if my laptop is stolen?
Now it is time we moved on to computers. We will begin with devices running the Windows operating system and use them as our reference point and make comparisons as we did with other similar platforms (in this case, Mac OS X, Chrome OS, and others)
- Microsoft (Windows):
Unfortunately, Windows falls short on many counts. If you use the platform and your device ever gets stolen, then you would not have much to stand on in such a scenario. Windows has always been a more vulnerable OS in terms of security flaws, bugs, and so on when compared to other operating systems, but its protection capabilities are probably worse.
Even the latest version of it that Microsoft released (Windows 10) failed to provide encryption for all categories of its users. The less said about the encryption abilities of older versions (like Windows 8.1, Windows Windows 7, Windows Vista, and Windows XP), the better.
In simple terms, for example, the drive that serves as storage space for your computer probably lacks encryption. What this means is that when your device gets stolen, the people who lay their hands on it can obtain access to your files, using some of the most basic approaches ever.
All they have to do is boot another operating system on it, and all restrictions disappear as if they were never there. In some cases, they could insert it into another PC and get it to work from there.
There might be some relief for a user who has a lot of money, but we cannot expect every individual to be precisely that kind of person. If you are using a feature-rich iteration of the operating system in view like the Enterprise, Professional, or Education edition of Windows 7, Windows 8, Windows 8.1, or Windows 10, then you can pay for encryption, using the optional BitLocker utility.
You can follow these instructions to find out if the BitLocker utility is available for you to make use of it on your computer.
- Open the Control Panel program. If you are running Windows 10, Windows 8.1 or Windows 8, you can do this by right-clicking on the Windows Start icon always visible on your desktop screen and selecting the required program from the Power User menu, which comprises of a good number of applications and optionsIf you are running an older version of Windows, you have to do things differently. Press the Windows button on your keyboard or click on the Windows Start icon to see a list of some programs. Select Control Panel
- After the Control Panel program window appears, you must click on System and Security. On the next screen, you must select BitLocker Drive Encryption. If you could not arrive at the stated destination, using the steps we just provided, then you must perform a search in the text field present using this keyword and click on the result that you need.

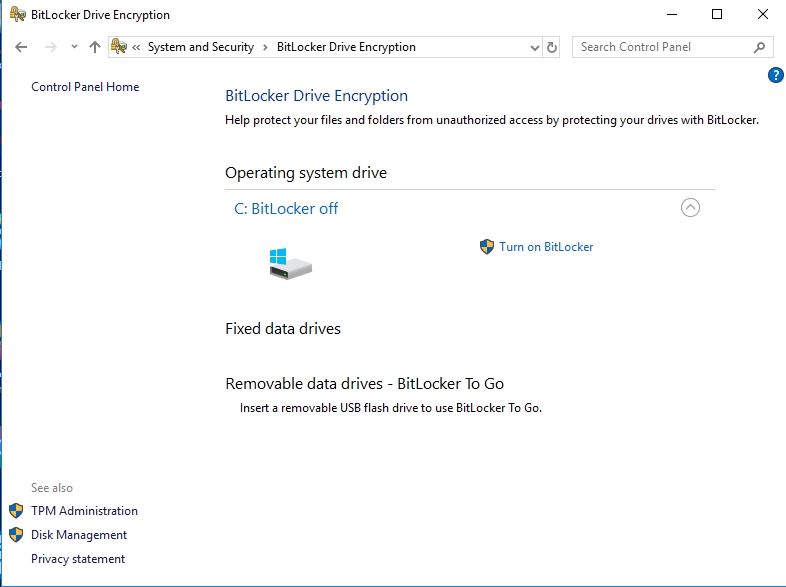
Encryption
If you could not find the stated utility no matter how hard you tried, then it is probably not available for you to employ—you are using a Home Edition of Windows. Unfortunately, it is not just standard stuff available for your device. Nevertheless, we know that some unique PCs (running Windows 8.1 or Windows 10) have recently been equipped with a similar albeit limited utility labeled Device Encryption.
The utility is a bit different in that it automatically encrypts your storage only if you sign into your computer, using a Microsoft account. Then again, we have to remind you that it is far from being readily available on the stated platforms. Better not to get your hopes up at all. If your computer possesses a unique or an exclusive set of hardware, then your chances of having it are good.
Follow these instructions to find out:
- Press (and hold) the Windows button on your keyboard, then tap the letter I key to launch the Settings app. After the program window comes up, you must click on System. On the next screen, click on About

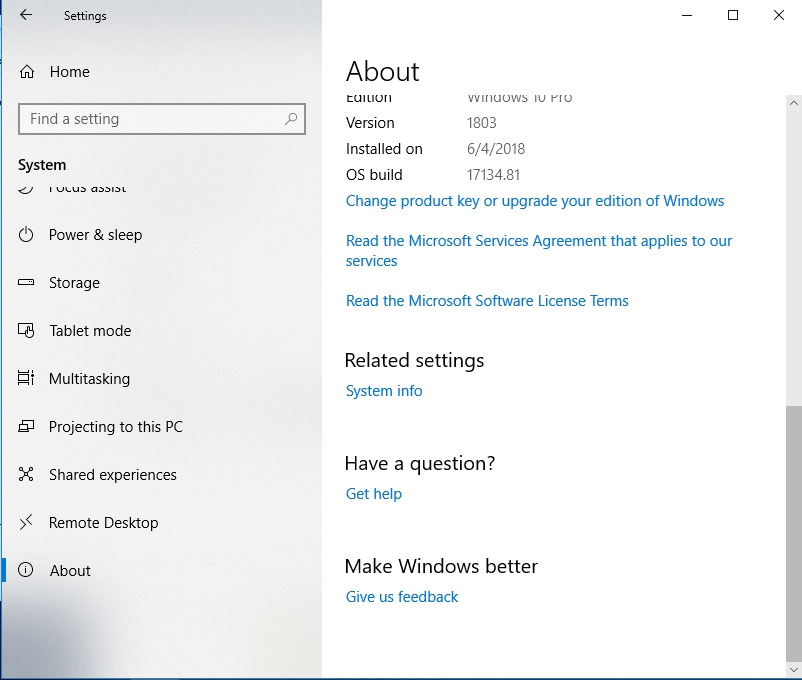
- In your current location, you should see some information about your PC. Check for any message that has something to do with Device Encryption with its keywords included as terms. If you find nothing, then it is time you gave up on using this utilityAlthough encryption is not really a strong suit on Windows, especially in terms of the functionalities it supports by default, it would be dishonest for us to leave out the fact that you could pay to get this capability. Numerous third-party apps are available for you to download and run. You can set up or customize them to suit your needs.Then again, we must avoid forgetting another vital fact in the midst of this entire squabble—you will only get encryption by making more effort than necessary or by going out of your way to acquire the needed functionality. Things are not meant to be this way.Regarding other features, you will get a bit more from Windows 10 at least. It is the latest version after all. On this version of Windows, Microsoft finally embedded its answer to utilities like Find My iPhone or Find My Android Device available on the IOS and Android platforms respectively. On your PC, there is a Find My Device tool you can employ to locate your computer if it gets stolen. You must have it enabled before the theft happened though.
- Apple (Mac OS X), Google (Chrome OS), and others:
In sharp contrast to the behavior exhibited by Microsoft in failing to provide encryption for all users of its operating system, Apple and Google do the right things on their non-mobile platforms (Mac OS X, and Chrome OS, respectively).
If you have a Mac, then you can rest in peace knowing that its internal disk is encrypted with FileVault. A thief cannot access your files or data if he/she does not know your password. There is a Find My Mac utility, which is very similar in terms of features and functionalities to the equivalent tools we described earlier.
The same story goes for Chromebooks. Systems running Linux are not far behind as all users on this platform can use the encryption option though there is the small bit of it not being set by default. It is all good though since it is far better from what you can get on Windows most times.
To conclude our views on the protection or security that Windows provides, we feel that it is unfortunate that Microsoft has not made encryption available for everyone by default. Due to this shortcoming or oversight, devices running the Windows OS are easily more vulnerable to data theft on average than others (unless Bit locker is enabled, but we know this is not the case in the vast majority of scenarios).
How to protect the data on your Windows when you travel?
If you came here to find out how to keep your data secure on your Windows laptop when traveling, then there are a couple of security recommendations besides the use of encryption which you must follow:
- Ensure that your device remains switched off whenever it is not in use
- Use a reliable and secure password to get into your OS, accounts on websites, and other platforms
- Regularly clear out your browser cache
- Use HTTPS always if possible
- Use a reliable VPN. You can make do with a proxy (if the first option is not available)
- Use two-factor authentication setup for all accounts and profiles, and so on
If you really care about what happens to the data on your system if it gets stolen, then it is logical for us to assume that PC protection is very high on your priority list. Therefore, we have to tell you that your computer’s security in the present is even more critical than what has got you worried. After all, some attackers do not even need to steal your device to gain access to your files, information or data.
For the stated reason, we recommend that you download and run Auslogics Anti-Malware to take your security setup to the highest level possible. This improvement might help ensure that you remain safe from all forms of threats.

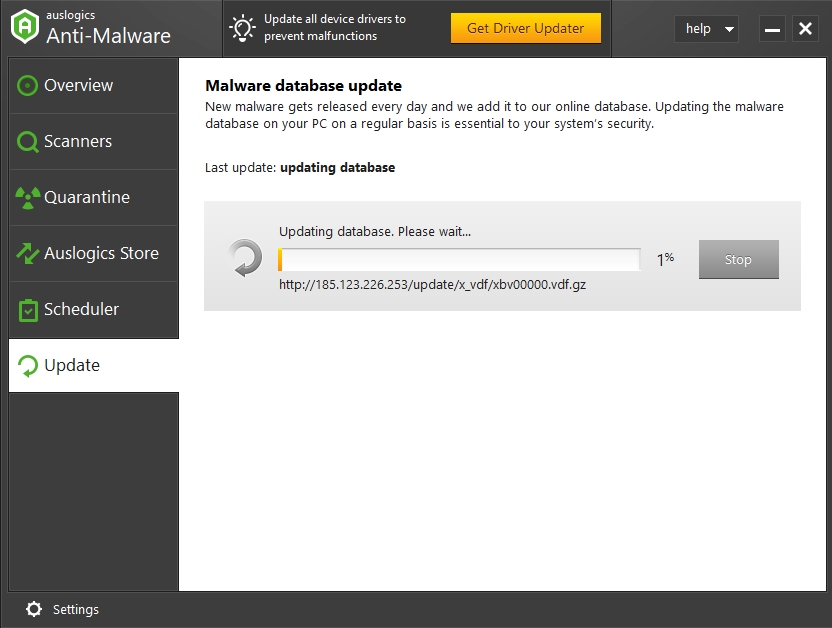
It does not matter if you already have an antivirus running. The recommended app is well capable of running alongside other security programs without causing problems. In fact, it probably would work in tandem with your antivirus and might help detect dangerous items that the latter missed. With this upgraded setup, you will become safer than ever.